Vehicle-infrastructure cooperative credible interaction method based on traffic business characteristics understanding
-
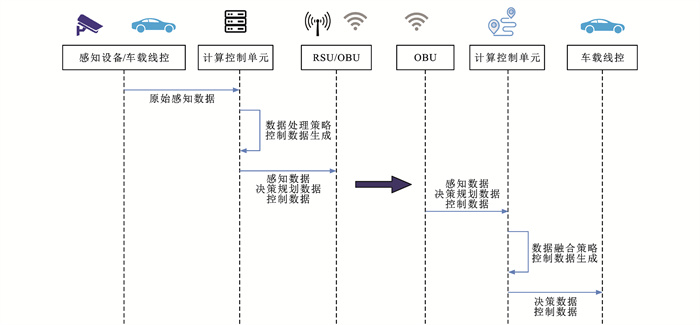
摘要: 为保障车路协同环境下信息的可信交互,分析了车车、车路协同信息交互流程和不同模式下的交互需求,设计了车路协同可信交互架构;构建了车辆行为状态推演模型与路径扰动因子量化模型,设计了车辆主体可信度计算方法与等级评估规则,实现了车辆主体行为可信认证;通过对交通业务的有效特征理解构建了消息紧急度量化模型,利用低分辨率筛选策略初步过滤了消息报文,基于支持向量机(SVM)对消息内容进行了深度理解,形成了多分辨率交互内容认知方法;使用包含OMNeT++和SUMO仿真模拟器的Veins搭建了仿真测试环境,针对不同网联自动驾驶车辆(CAV)渗透率下的开放道路和交叉口场景开展了仿真试验,对提出的车路协同可信交互方法进行了测试验证。研究结果表明:结合交通业务特征理解能够有效改善车路协同信息交互的可信度判别,提出的方法对信标位置消息的平均认知正确率可以达到90.91%,相比基于时效性检测的可信交互方法提高了8.68%;在安全效率消息可信交互验证试验中,随着恶意车辆比例的增加,传统基于投票机制的车路协同可信交互方法逐渐失效,而提出的方法在保证单次认证时延小于13 ms的条件下,平均正确率达到94.96%,较传统基于反向传播(BP)神经网络的方法提高了3.05%,且CAV渗透率越大,可信交互检测结果的准确率越高,漏报率越低,能够满足车路协同可信交互需求。Abstract: For the credible information interaction in vehicle-infrastructure cooperative environments, the processes of vehicle-vehicle and vehicle-infrastructure cooperative information interaction and the interaction requirements of different modes were analyzed, and a vehicle-infrastructure cooperative credible interaction framework was designed. A model of vehicle behavior state deduction and one of path perturbation factor quantification were constructed. A credibility calculation method for the vehicle object and level evaluation rules were designed. The credible authentication of vehicle object behavior was thereby achieved. A quantification model for the message urgency was built by understanding the effective traffic business characteristics. The low-resolution filtering strategy was used to preliminarily filter the message, and the message content was deeply understood on the basis of the support vector machine (SVM), thereby obtaining a multi-resolution interactive content cognition method. The Veins with OMNeT++ and SUMO simulators was used to build a simulation test environment. Simulation tests were carried out in open roads and intersection scenarios with different penetration rates of connected and automated vehicles (CAVs). The proposed vehicle-infrastructure cooperative credible interaction method was tested and verified. Research results show that the credibility identification for the vehicle-infrastructure cooperative information interaction can be effectively improved by understanding the traffic business characteristics. The average cognitive accuracy for the beacon location message achieved by the proposed method is 90.91%. It is 8.68% higher than that of the credible interaction method based on the timeliness detection. In the credible interaction verification experiment on the safety efficiency message, as the proportion of malicious vehicles increases, the traditional vehicle-infrastructure cooperative credible interaction method based on the voting mechanism is gradually held invalid. In contrast, an average accuracy of 94.96% is achieved by the proposed method under the condition that the single authentication delay is less than 13 ms. It is 3.05% higher than that of the traditional method based on the back propagation (BP) neural network. Moreover, a higher accuracy rate and a lower false negative rate of the credible interaction detection results can be obtained with a higher CAV penetration rate. Therefore, the needs of vehicle-infrastructure cooperative credible interaction can be met by the proposed method.
-
表 1 车辆类型与初始可信度的映射关系
Table 1. Mapping relationship between vehicle type and initial credibility
初始可信等级 车辆类型 初始信任程度 λ P1 交管车、消防车、警车、救护车 可信 1.0 P2 公交车、出租车、网约车等 比较可信 0.8 P3 城管、水电城市公共设施维修车辆 基本可信 0.6 P4 私人车、单位车等普通车辆 不太可信 0.4 P5 故障、攻击或没进行年检的车等 不可信 0.2 表 2 开放道路仿真参数
Table 2. Simulation parameters of open road
项目 数值 车辆运行车道数 4 车辆运行长度/m 300 车辆长度/m 4 行驶车辆数/veh 100 最大行驶速度/(km·h-1) 80 最小行驶速度/(km·h-1) 0 最大加速度/(m·s-2) 2.5 最大减速度/(m·s-2) 9 初始速度/(km·h-1) 30 表 3 信号交叉口仿真参数
Table 3. Simulation parameters of signalized intersection
项目 数值 车辆运行车道数 4 车辆运行长度/m 600 车辆长度/m 4 行驶车辆数/veh 500 最大行驶速度/(km·h-1) 50 最小行驶速度/(km·h-1) 0 最大加速度/(m·s-2) 2.5 最大减速度/(m·s-2) 9 初始速度/(km·h-1) 30 表 4 车辆状态推演误差对比
Table 4. Comparison of vehicle state deduction errors
% 推演方法 平均绝对相对误差 最大绝对相对误差 畅通时段 高峰时段 畅通时段 高峰时段 本文方法 1.85 5.21 5.87 11.25 多元非线性拟合 1.93 5.89 5.32 12.58 表 5 消息分类结果混淆矩阵
Table 5. Confusion matrix of message classification results
实际类别 分类结果 无效消息 有效消息 无效消息 A1 A2 有效消息 A3 A4 表 6 开放道路混合交通场景
Table 6. Heterogeneous traffic scenario of open road
% 交通场景 CAV占比 AHDV占比 CHDV占比 占比总计 路段场景1 25.0 37.5 37.5 100.0 路段场景2 50.0 25.0 25.0 100.0 路段场景3 75.0 12.5 12.5 100.0 路段场景4 100.0 0.0 0.0 100.0 表 7 信号交叉口混合交通场景
Table 7. Heterogeneous traffic scenarios of signalized intersection
% 交通场景 CAV占比 HDV1占比 HDV2占比 HDV3占比 HDV4占比 占比总计 交叉口场景1 25.00 18.75 18.75 18.75 18.75 100.00 交叉口场景2 50.00 12.50 12.50 12.50 12.50 100.00 交叉口场景3 75.00 6.25 6.25 6.25 6.25 100.00 交叉口场景4 100.00 0.00 0.00 0.00 0.00 100.00 -
[1] CHEN Wei, GUO Fang-zhou, WANG Fei-yue. A survey of traffic data visualization[J]. IEEE Transactions on Intelligent Transportation Systems, 2015, 16(6): 2970-2984. doi: 10.1109/TITS.2015.2436897 [2] YAO De-zhong, YU Chen, YANG L T, et al. Using crowdsourcing to provide QoS for mobile cloud computing[J]. IEEE Transactions on Cloud Computing, 2019, 7(2): 344-356. doi: 10.1109/TCC.2015.2513390 [3] 马永杰, 程时升, 马芸婷, 等. 卷积神经网络及其在智能交通系统中的应用综述[J]. 交通运输工程学报, 2021, 21(4): 48-71. doi: 10.19818/j.cnki.1671-1637.2021.04.003MA Yong-jie, CHENG Shi-sheng, MA Yun-ting, et al. Review of convolutional neural network and its application in intelligent transportation system[J]. Journal of Traffic and Transportation Engineering, 2021, 21(4): 48-71. (in Chinese) doi: 10.19818/j.cnki.1671-1637.2021.04.003 [4] LI Wen-jia, SONG Hou-bing. ART: an attack-resistant trust management scheme for securing vehicular ad hoc networks[J]. IEEE Transactions on Intelligent Transportation Systems, 2016, 17(4): 960-969. doi: 10.1109/TITS.2015.2494017 [5] LU Zhao-jun, QU Gang, LIU Zheng-lin. A survey on recent advances in vehicular network security, trust, and privacy[J]. IEEE Transactions on Intelligent Transportation Systems, 2019, 20(2): 760-776. doi: 10.1109/TITS.2018.2818888 [6] 张毅, 姚丹亚, 李力, 等. 智能车路协同系统关键技术与应用[J]. 交通运输系统工程与信息, 2021, 21(5): 40-51. doi: 10.16097/j.cnki.1009-6744.2021.05.005ZHANG Yi, YAO Dan-ya, LI Li, et al. Technologies and applications for intelligent vehicle-infrastructure cooperation systems[J]. Journal of Transportation Systems Engineering and Information Technology, 2021, 21(5): 40-51. (in Chinese) doi: 10.16097/j.cnki.1009-6744.2021.05.005 [7] DENG Ruo-qi, DI Bo-ya, SONG Ling-yang. Cooperative collision avoidance for overtaking maneuvers in cellular V2X-based autonomous driving[J]. IEEE Transactions on Vehicular Technology, 2019, 68(5): 4434-4446. doi: 10.1109/TVT.2019.2906509 [8] 赵祥模, 惠飞, 史昕, 等. 泛在交通信息服务系统的概念、架构与关键技术[J]. 交通运输工程学报, 2014, 14(4): 105-115. http://transport.chd.edu.cn/article/id/201404013ZHAO Xiang-mo, HUI Fei, SHI Xin, et al. Concept, architecture and challenging technologies of ubiquitous traffic information service system[J]. Journal of Traffic and Transportation Engineering, 2014, 14(4): 105-115. (in Chinese) http://transport.chd.edu.cn/article/id/201404013 [9] CHETLUR V V, DHILLON H S. Coverage and rate analysis of downlink cellular vehicle-to-everything (C-V2X) communication[J]. IEEE Transactions on Wireless Communications, 2020, 19(3): 1738-1753. doi: 10.1109/TWC.2019.2957222 [10] ALNASSER A, SUN Hong-jian, JIANG Jing. Cyber security challenges and solutions for V2X communications: a survey[J]. Computer Networks, 2019, 151: 52-67. doi: 10.1016/j.comnet.2018.12.018 [11] AL-SULTAN S, Al-DOORI M M, AL-BAYATTI A H, et al. A comprehensive survey on vehicular ad hoc network[J]. Journal of Network and Computer Applications, 2014, 37: 380-392. doi: 10.1016/j.jnca.2013.02.036 [12] 上官伟, 史斌, 蔡伯根, 等. 车路协同环境下信道接入协议的优化方法[J]. 交通运输系统工程与信息, 2016, 16(6): 47-53. doi: 10.3969/j.issn.1009-6744.2016.06.008SHANGGUAN Wei, SHI Bin, CAI Bai-gen, et al. Optimization of channel access protocols and performance evaluation in cooperative vehicle infrastructure environment[J]. Journal of Transportation Systems Engineering and Information Technology, 2016, 16(6): 47-53. (in Chinese) doi: 10.3969/j.issn.1009-6744.2016.06.008 [13] GHOSAL A, CONTI M. Security issues and challenges in V2X: a survey[J]. Computer Networks, 2020, 169: 107093. doi: 10.1016/j.comnet.2019.107093 [14] 蔡伯根, 王丛丛, 上官伟, 等. 车路协同系统信息交互仿真方法[J]. 交通运输工程学报, 2014, 14(3): 111-119. doi: 10.3969/j.issn.1671-1637.2014.03.020CAI Bai-gen, WANG Cong-cong, SHANGGUAN Wei, et al. Simulation method of information interaction in CVIS[J]. Journal of Traffic and Transportation Engineering, 2014, 14(3): 111-119. (in Chinese) doi: 10.3969/j.issn.1671-1637.2014.03.020 [15] LI Teng-long, HUI Fei, ZHAO Xiang-mo, et al. Modelling heterogeneous traffic dynamics by considering the influence of V2V safety messages[J]. IET Intelligent Transport Systems, 2020, 14(4): 220-227. doi: 10.1049/iet-its.2019.0361 [16] RAWAT D B, POPESCU D C, YAN Gong-jun, et al. Enhancing VANET performance by joint adaptation of transmission power and contention window size[J]. IEEE Transactions on Parallel and Distributed Systems, 2011, 22(9): 1528-1535. doi: 10.1109/TPDS.2011.41 [17] 刘云璐, 蒲菊华, 方维维, 等. 一种无线传感器网络MAC协议优化算法[J]. 计算机学报, 2012, 35(3): 529-539. https://www.cnki.com.cn/Article/CJFDTOTAL-JSJX201203012.htmLIU Yun-lu, PU Ju-hua, FANG Wei-wei, et al. A MAC layer optimization algorithm in wireless sensor networks[J]. Chinese Journal of Computers, 2012, 35(3): 529-539. (in Chinese) https://www.cnki.com.cn/Article/CJFDTOTAL-JSJX201203012.htm [18] TAN Shuai-shuai, LI Xiao-ping, DONG Qing-kuai. Trust based routing mechanism for securing OSLR-based MANET[J]. Ad Hoc Networks, 2015, 30: 84-98. doi: 10.1016/j.adhoc.2015.03.004 [19] VIJAYAKUMAR P, AZEES M, KANNAN A, et al. Dual authentication and key management techniques for secure data transmission in vehicular ad hoc networks[J]. IEEE Transactions on Intelligent Transportation Systems, 2016, 17(4): 1015-1028. doi: 10.1109/TITS.2015.2492981 [20] VIJAYAKUMAR P, AZEES M, CHANG V, et al. Computationally efficient privacy preserving authentication and key distribution techniques for vehicular ad hoc networks[J]. Cluster Computing, 2017, 20(3): 2439-2450. doi: 10.1007/s10586-017-0848-x [21] AZEES M, VIJAYAKUMAR P, DEBOARH L J. EAAP: efficient anonymous authentication with conditional privacy-preserving scheme for vehicular ad hoc networks[J]. IEEE Transactions on Intelligent Transportation Systems, 2017, 18(9): 2467-2476. doi: 10.1109/TITS.2016.2634623 [22] 季一木, 陆毅成, 刘尚东, 等. HIBE-MPJ: 一种基于HIBE的物联网环境下跨域通信机制研究[J]. 南京邮电大学学报(自然科学版), 2020, 40(4): 1-10. https://www.cnki.com.cn/Article/CJFDTOTAL-NJYD202004001.htmJI Yi-mu, LU Yi-cheng, LIU Shang-dong, et al. HIBE-MPJ: cross-domain communication mechanism based on HIBE in Internet of things environment[J]. Journal of Nanjing University of Posts and Telecommunications (Natural Science Edition), 2020, 40(4): 1-10. (in Chinese) https://www.cnki.com.cn/Article/CJFDTOTAL-NJYD202004001.htm [23] 郑明辉, 段洋洋, 吕含笑. 车联网中基于群签名的身份认证协议研究[J]. 工程科学与技术, 2018, 50(4): 130-134. https://www.cnki.com.cn/Article/CJFDTOTAL-SCLH201804017.htmZHENG Ming-hui, DUAN Yang-yang, LYU Han-xiao. Research on identity authentication protocol group signature-based in Internet of vehicles[J]. Advanced Engineering Sciences, 2018, 50(4): 130-134. (in Chinese) https://www.cnki.com.cn/Article/CJFDTOTAL-SCLH201804017.htm [24] 杨雪婷, 李重. 车联网中基于车辆行为预测的身份认证方案[J]. 计算机工程, 2021, 47(1): 129-138. https://www.cnki.com.cn/Article/CJFDTOTAL-JSJC202101018.htmYANG Xue-ting, LI Zhong. Identity authentication scheme based on vehicle behavior prediction for IoV[J]. Computer Engineering, 2021, 47(1): 129-138. (in Chinese) https://www.cnki.com.cn/Article/CJFDTOTAL-JSJC202101018.htm [25] VUKADINOVIC V, BAKOWSKI K, MARSCH P, et al. 3GPP C-V2X and IEEE 802.11p for vehicle-to-vehicle communications in highway platooning scenarios[J]. Ad Hoc Networks, 2018, 74: 17-29. [26] SHAIKH R A, ALZAHRANI A S. Intrusion-aware trust model for vehicular ad hoc networks[J]. Security and Communication Networks, 2014, 7(11): 1652-1669. [27] ARSHAD M, ULLAH Z, AHMAD N, et al. A survey of local/cooperative-based malicious information detection techniques in VANETs[J]. EURASIP Journal on Wireless Communications and Networking, 2018, 2018: 62. [28] KIM T H J, STUDER A, DUBEY R, et al. VANET alert endorsement using multi-source filters[C]//ACM. Proceedings of the Seventh ACM International Workshop on Vehicular Internetworking. New York: ACM, 2010: 51-60. [29] YAO Xuan-xia, ZHANG Xin-lei, NING Huan-sheng, et al. Using trust model to ensure reliable data acquisition in VANETs[J]. Ad Hoc Networks, 2017, 55: 107-118. [30] 刘伎昭, 董跃钧. 基于空间推理的车联网虚假消息检测方法[J]. 计算机工程与设计, 2020, 41(12): 35-39. https://www.cnki.com.cn/Article/CJFDTOTAL-SJSJ202012005.htmLIU Ji-zhao, DONG Yue-jun. False messages detection method based on spatial inference in Internet of vehicles[J]. Computer Engineering and Design, 2020, 41(12): 35-39. (in Chinese) https://www.cnki.com.cn/Article/CJFDTOTAL-SJSJ202012005.htm [31] MUHAMMAD M, SAFDAR G A. Survey on existing authentication issues for cellular-assisted V2X communication[J]. Vehicular Communications, 2018, 12: 50-65. -





 下载:
下载: